In The State of Ransomware 2020 report, over half the participating companies surveyed across 26 countries reported that they had been hit by ransomware in the past 12 months. This result demonstrates the critical need for predictive zero-day threat identification and protection as advanced threats like ransomware become more targeted and evasive.
Sophos XG Firewall offers several pre-configured templates to create a protection rule for commonly used non-HTTP applications and services. You can use these templates to create a rule for the web application, that is close to your configuration, then modify it to fit your needs.
- To update the web admin console settings, go to Administration Admin and user settings. To access the sign-in window, open a browser and type the internal IP address or the hostname of XG Firewall in the address bar, followed by the port number if it differs from 443. Example: security.sophos.com:4444.
- Sophos XG Web Application Firewall configuration steps. The Damn Vulnerable Web Application (DVWA) is a great place to start since it allows for multiple exploits with differing levels or native protection.
The next thing in next-gen: Ultimate enterprise firewall performance, security, and control. The all-new Sophos Firewall OS integrates all the advanced networking, protection, use. Advanced Threat Protection (Detect and block network traffic attempting to contact command and control servers using multi-layered DNS, AFC, and firewall) Sophos Security Heartbeat™ instantly identifies compromised endpoints including the host, user, process, incident count,.
In this fourth in our series of articles on making the most of the great new features in XG Firewall v18, we’re going to specifically focus on the new capabilities in XG Firewall v18 designed to protect against the latest zero-day threats such as new ransomware variants.
Xstream Threat Protection
In previous articles, we covered the Xstream architecture and the new DPI engine, the new TLS inspection solution, and the Network Flow FastPath. These all play a critical role in identifying and stopping the latest zero-day threats. This article highlights the new cloud-based Threat Intelligence and Sandstorm sandboxing technologies which are part of the Sandstorm Protection subscription.
How it works:
XG Firewall v18 includes new machine learning (ML) based threat intelligence and a newly enhanced version of Sandstorm sandboxing, which work together to identify the latest zero-day threats. Both are powered by SophosLabs Intelix, which uses machine learning technology, decades of threat research, and petabytes of intelligence to provide unmatched protection against new and previously unseen threats.
When XG Firewall’s Xstream DPI engine performs AV analysis on a file entering the network and determines there is active code, it holds the file temporarily and sends it to the SophosLabs Intelix service in the cloud for both static and dynamic (sandbox) analysis. It then provides a detailed overview of the results and only releases the file to the downloader or email recipient if the file is declared safe.
This last step is important, as many advanced malware solutions on firewalls release a file to the end-user before the analysis is complete, potentially resulting in an extensive and expensive cleanup if the file is then ultimately convicted as a threat once all analysis is finished.
Let’s take a look at what happens to a file that is scanned in a bit more detail:
Threat intelligence analysis:
Threat intelligence uses multiple machine learning models to analyze the characteristics, features, genetics, and global reputation of the file. It compares the new file with millions of known good and bad files in the SophosLabs database to render a verdict in seconds without the need to execute it in real time. This makes it remarkably fast and effective at identifying new threats and new variants of existing threats, particularly with files which are not easily sandboxed, such as password-protected documents.
Sandstorm sandboxing analysis:
At the same time a file is submitted for threat intelligence analysis, it is also submitted for dynamic behavioral analysis in our cloud sandbox environment. Because it’s cloud-based, there’s no additional software or hardware required, and no impact on firewall performance.
To identify threats based on their behavior, SophosLabs has integrated the latest protection technologies from our industry-leading Intercept X next-gen endpoint product into the Sophos Sandstorm sandbox. This includes deep learning analysis, exploit detection, and CryptoGuard to detect active ransomware encrypting files in real time. The sandbox also monitors all file, memory, registry, and network activity as well as sandbox evasion techniques. No other firewall can offer this kind of run-time analysis with the world’s best threat protection, Intercept X. And no other firewall offers the level of insight and reporting that XG Firewall provides – including a time-lapse series of screen shots showing events during the file execution.
Sandboxing is particularly effective at detecting threats that can lurk in normally benign files that may not have any obvious malicious characteristics. Office files with macros or benign executables and application updates that have been subverted by hackers are prime candidates for detection through sandboxing.
How to make the most of Xstream Threat Protection
There are three key things you need to enable this critically important protection:
- Ensure your XG Firewall license includes the Web Protection and Sandstorm Protection subscriptions. You need both of these subscriptions active to be protected from the latest threats. The new threat intelligence analysis in XG Firewall v18 is part of the Sandstorm license, adding tremendous value over the previous version at no extra cost. Log into your XG Firewall and go to the Administration menu to see a list of your active subscriptions. Be sure to contact your preferred Sophos Partner immediately if you don’t have both these protection subscriptions active.
- The new threat protection technology in XG Firewall can only inspect and analyze decrypted traffic, so ensure that you’re inspecting TLS-encrypted web traffic. With the vast majority of web traffic now encrypted, it’s critical that you decrypt and inspect files being downloaded onto your network to have them analyzed for potential threats. Check our recent article on the high-performance TLS inspection solution in XG Firewall v18 for full details on how to take advantage of this great new capability.
- In all firewall rules governing web traffic for your network, ensure you have the following two web filtering security options set to scan web traffic and use the latest zero-day protection technologies outlined here:
That’s it – it’s really that easy!
Check out this video for an in-depth guide on making the most of this new feature, a detailed look at the new and improved threat intelligence reporting, and how to interpret the results:
Testing it yourself
Sophos Web Protection Bypass
There’s a convenient and harmless test file you can find at SophosTest.com, which will provide a sample report for you to review.
Also, keep an eye on your Control Center widget for any recent file downloads that have been analyzed and then drill down for further details.
When you click the Control Center widget (highlighted above), you can drill down into a detailed list of files analyzed and their results. Mouse over the results column to display the threat meter, which provides a good high-level overview of the analysis results (as shown below).
Here’s a summary of the resources available to help you make the most of the new features in XG Firewall v18, including the new zero-day threat protection capabilities:
If you’re new to Sophos XG Firewall, learn more about the great benefits and features XG Firewall can deliver to your network.
XG Firewall makes it simple to get up and running quickly with the best network visibility, protection, and response in the industry. We make it easy to protect your network across multiple sites while also enabling access for your remote workers.
Getting started
Deployment
If you just received your XG Firewall, run through the convenient XG Firewall setup wizard which will have you up and running in a few minutes with essential protection for your network.
If you are running two XG Firewall appliances in High Availability mode for maximum business continuity, then be sure to take advantage of the new Quick HA option in v18.
INSTRUCTIONS: ‘How to deploy in gateway mode’ ► VIDEO ‘Registration and setup wizard’ ►
Get familiar with XG firewall
After the initial setup, review our extensive library of Getting Started How-To videos and the Documentation for XG Firewall. There’s also a great list of articles and videos to review on the Initial Setup Community Forum.
Periodic best practices checkup
To ensure your XG Firewall is protecting your network optimally, follow these best practices after initial setup or periodically.
If you don’t have time to perform these steps, the Sophos Professional Services team of network experts is available to help ensure your firewall is configured optimally. Contact them at professionalservices@sophos.com.
Double check your protection licenses
On your XG Firewall go to Administration > Licensing and ensure you have these essential network protection subscriptions:
- Network Protection – Essential for IPS, advanced threat protection, and botnet protection
- Web Protection – Essential for web security and control and application control
- Sandstorm Protection – Essential for the latest threat protection using artificial intelligence and sandboxing analysis
- Email Protection – Essential for anti-spam and phishing attack protection
- Web Server Protection – Essential if you have any servers that require public internet access
Update firmware
Always keep your firmware up to date to ensure you have the latest security, performance, and reliability updates. You can get the latest v18 release for your XG Firewall from MySophos.
INSTRUCTIONS: ‘How to download firmware updates’ ► VIDEO: ‘Firmware update and roll-back’ ►

Firewall rule and protection policy recommendations
Of course, by design, your firewall blocks all network traffic – your network is completely locked down – but you enable traffic to flow by creating firewall rules.
Firewall rules enable your network to function, but they also create opportunities for hackers, ransomware, and malware to enter. Hence, it’s essential to protect your network by applying security policies to these firewall rules.
If you’re new to XG Firewall or v18, check out the introductory video on Firewall Rules and the What’s new in v18 for Firewall Rules video.
If your firewall has been running for a while, you may have dozens or even hundreds of firewall rules you’ve added over time. It’s very important that you periodically review all your firewall rules to ensure that there are no avoidable “openings” in your network. Ensure you don’t have any unnecessary or unused rules that are presenting openings that hackers can take advantage of.
Start by checking the ‘Active firewall rules’ widget on the Control Center to identify unused rules:
Then, go through your firewall rules to examine all the active rules to ensure they are needed and proper protection is being applied.
In particular, disable all non-essential port-forwarding rules, and re-evaluate if any of the port-forwarding rules you have can be better accommodated via VPN access or, at the very least, multifactor authentication.
Exposed services and servers through port forwarding are one of the top ways hackers breach your network. VPN and MFA provide much better security for remote access to internal network resources.
If you are on v17.x we suggest you upgrade to v18 for the latest NAT rule enhancements. If you are on v18 already, review all your NAT rules to ensure all are required and adequately protected by a corresponding firewall rule.
Make sure you’re applying essential protection to all your firewall rules. XG Firewall makes it super easy to assign web protection and control, intrusion prevention (IPS), sandboxing, and file analysis as well as application control.
In general, do not apply “Allow All” or “None” when selecting a protection policy. These should only be used in special circumstances or for troubleshooting, never as an active protection policy.
Recommended protection best practices
TLS Inspection
Download djvu for mac free. Most internet traffic is encrypted with SSL/TLS making it impossible to secure without proper inspection.
XG Firewall v18 introduced the new Xstream TLS Inspection feature that provides high-performance inspection of encrypted traffic, enabling you to properly protect your network. Ensure you have one or more TLS inspection rules applied to your internet traffic, otherwise a lot of the protection discussed below will be ineffective. (Instructions: ‘SSL/TLS inspection rules’ / Video: ‘Xstream SSL inspection in XG Firewall v18′).
You will need to deploy the XG Firewall SSL certificate on your client machines, which is accomplished easiest on Windows using the wizard in Microsoft’s Group Policy Manager.
After deployment, monitor TLS inspection via the Control Center and add important problematic sites to the exception list with the convenient tools available from the widget.
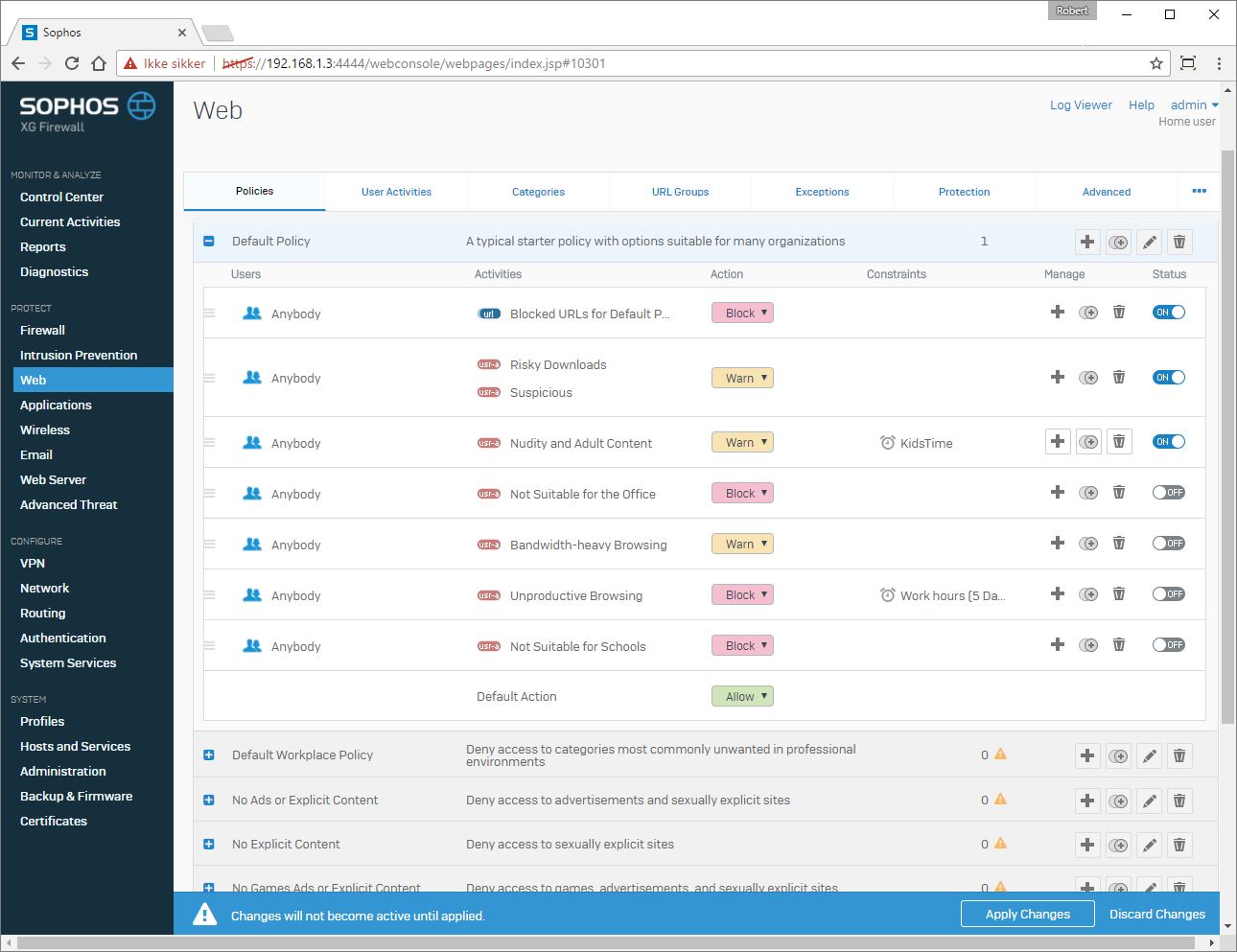
Web policy and protection

This determines which websites are allowed or blocked and how to protect web traffic. Any firewalls governing internet traffic should have a web filtering policy in place.
There are several built-in policies for schools, workplaces, and more that you can use out-of-the-box to make this easy. Simply choose one appropriate for your organization and customize it to suit your needs. (Instructions: ‘How to implement Web Protection’ instructions / Video: ‘How To: Creating Web Protection rules’).
Malware and content scanning
XG Firewall can scan all web traffic for malicious code and downloaded files.
We strongly recommend that you take advantage of SophosLabs Threat Intelligence and Sophos Sandstorm sandboxing to further analyze files.
To do so, simply check the option to “Detect zero-day threats with Sandstorm” for all rules governing web traffic. (Instructions: ‘How to configure Sophos Sandstorm’).
IPS
Sophos Web Protection Test Page
Intrusion Prevention looks for activity attempting to exploit vulnerabilities in networked devices. This is a common technique for hackers to get control of servers exposed to the internet and to move laterally within a network. IPS protection signatures are included for all platforms: Windows, Macs, Unix, and more.
Make sure you are applying IPS protection policies that align with the network platforms in your environment – use either one of the built-in policies or create your own. Also, ensure you not only apply IPS protection to internet traffic rules but also rules between different segments of your internal network (e.g. LAN and DMZ) to help catch active threats trying to spread on your network. (Instructions: ‘IPS policies’ / Video: ‘How To: Setting Up And Configuring IPS’).
ATP
Advanced Threat Protection is another essential aid in identifying an active threat on your network. It examines outbound traffic for any attempts to contact known hacker command and control servers.
If an ATP is detected, it indicates you have a bot or threat on your network. ATP setup is super easy. (Instructions: ‘How to configure Advanced Threat Protection (ATP)’).
Firewall best practices for blocking ransomware
Check out this white paper on additional best practices for blocking Ransomware attacks.
VPN connectivity recommendations
With VPN connections being tremendously important these days, here are some additional resources on getting the most from your XG Firewall’s VPN connectivity options.
Site-to-Site VPN: If you want the ultimate in VPN reliability and security between your central office and branch offices or remote locations, Sophos unique RED tunnels are ideal. How do i free up internal storage on my android phone.
Sophos Xg Web Protection App
You can easily deploy an XG Firewall to a remote location without touching it and set up a RED tunnel in no time. (Instructions: ‘Substituting XG for RED devices via Light-Touch deployment from Sophos Central’).
Remote user VPN: If you have users working remotely, XG Firewall offers a couple of options for secure remote access.
Our previous article outlined the various access options and their pros/cons. We recommend using Sophos Connect Client for the ultimate in ease-of-use. (Instructions: ‘Sophos Connect Client’ / Video: ‘Sophos Connect VPN Client’).
Helpful resources
Customer Resource Center (how-to videos, documentation, and more)
How-To Video Library (dozens of video tutorials to get you started)
XG Community (tap into the vast knowledge and expertise of the XG Firewall community)
